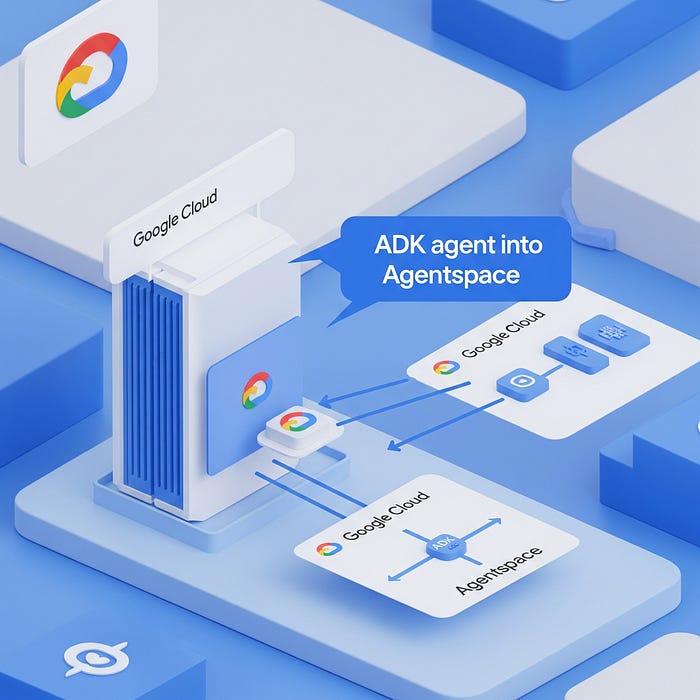
This post outlines the steps required to deploy an Agent Development Kit (ADK) Agent from Agent Engine to Agentspace.
Hopefully Google publish some docs on how to do this and thanks to Andy Hood for figuring this out. If you do need help with this reach out via https://aviato.consulting
Follow these instructions carefully to ensure a successful deployment.
Note
Both Agent Engine and AgentSpace have been recently renamed as part of Google’s AI branding, so you will still see references in the APIs to their previous names:
- Agent Engine: was formerly known as Reasoning Engine
- Agentspace: was formerly known as Discovery Engine
Prerequisites
Before beginning the deployment process, ensure you have the following:
- ADK Agent deployed to Agent Engine: A fully developed and tested ADK Agent has been deployed to Agent Engine
Instructions for developing and deploying the ADK Agent are outside of the scope of this document.
- Agentspace Account: An active Agentspace account with the necessary permissions to deploy agents.
- Credentials: Valid credentials for authenticating with Agentspace.
Deployment Steps
The deployment process involves several key steps:
Step 1: ADK Agent deployed to Agent Engine
- Obtain the Id of the deployed ADK Agent: You can obtain the ID via the Google Cloud Console or by using the following Agent Engine:List REST API:
LOCATION=us-central1
PROJECT_ID=aviato-project-id
TOKEN=$(gcloud auth print-access-token)
curl -X GET "https://$LOCATION-aiplatform.googleapis.com/v1/projects/$PROJECT_ID/locations/$LOCATION/reasoningEngines" \
- header "Authorization: Bearer $TOKEN"
Response (truncated):
{
"reasoningEngines": [
{
"name": "projects/123456789/locations/us-central1/reasoningEngines/123456789",
"displayName": "ADK Short Bot",
"spec": {
…
}
Note: when obtaining the ID via the Google Cloud Console, the ID may have the Project Id in the resource name. The AgentSpace API appears to require the Project Number instead.
Step 2: Obtain the Id of your AgentSpace application
Option 1: Use the AgentSpace menu in the Google Cloud Console to obtain the ID of your AgentSpace application:
Option 2: Use the AgentSpace List Engines REST API to list the current AgentSpace applications in your project:
# Note AgentSpace currently only supports the global, us and eu multi-regions
LOCATION=global
PROJECT_ID=aviato-project-id
TOKEN=$(gcloud auth print-access-token)
curl -X GET "https://discoveryengine.googleapis.com/v1alpha/projects/$PROJECT_ID/locations/$LOCATION/collections/default_collection/engines" \
- header "Authorization: Bearer $TOKEN" \
- header "x-goog-user-project: $PROJECT_ID"
Response (truncated):
{
"engines": [
{
"name": "projects/123456789/locations/global/collections/default_collection/engines/agentspace-andy_123456789",
"displayName": "Agentspace - Andy",
"createTime": "2025–06–05T22:55:44.459263Z",
…
}
Important Notes
- If you receive an error saying “Your application is authenticating by using local Application Default Credentials. The discoveryengine.googleapis.com API requires a quota project, which is not set by default” then make sure you have added the x-goog-user-project header.
- In the REST API, the collection name uses a hard coded default of default_collection.
Step 3: Publish the Agent Engine ADK Agent to AgentSpace application
The below requires the Project Number, e.g. 123456789, instead of the Project Id, e.g. aviato-project. To obtain the project number use:
gcloud projects describe PROJECT_ID
Use the AgentSpace Create Agent REST API to publish your Agent Engine ADK Agent to your AgentSpace application. In the body of the POST request, ensure that you replace the reasoningEngine name with the ID returned in Step 1.
# Note AgentSpace currently only supports the global, us and eu multi-regions
LOCATION=global
PROJECT_ID=aviato-project-id
TOKEN=$(gcloud auth print-access-token)
# Use the AgentSpace Application ID returned in the previous step
AGENTSPACE_ID=agentspace-andy_1749164028618
curl -X POST "https://discoveryengine.googleapis.com/v1alpha/projects/$PROJECT_ID/locations/$LOCATION/collections/default_collection/engines/$AGENTSPACE_ID/assistants/default_assistant/agents" \
- header "Authorization: Bearer $TOKEN" \
- header "x-goog-user-project: $PROJECT_ID" \
- data '{
"displayName": "My ADK Agent",
"description": "Description of the ADK Agent",
"adkAgentDefinition": {
"tool_settings": {
"tool_description": "Tool Description"
},
"provisionedReasoningEngine": {
"reasoningEngine": "projects/123456789/locations/us-central1/reasoningEngines/123456789"
}
}
}'
Response:
{
"name": "projects/123456789/locations/global/collections/default_collection/engines/agentspace-andy_1749164028618/assistants/default_assistant/agents/123456789",
"displayName": "My ADK Agent",
"description": "Description of the ADK Agent",
"adkAgentDefinition": {
"toolSettings": {
"toolDescription": "Tool description"
},
"provisionedReasoningEngine": {
"reasoningEngine": "projects/123456789/locations/us-central1/reasoningEngines/123456789"
}
},
"state": "CONFIGURED"
}
Important Notes
- If you receive an error saying “Your application is authenticating by using local Application Default Credentials. The discoveryengine.googleapis.com API requires a quota project, which is not set by default” then make sure you have added the x-goog-user-project header to the REST API
- In the REST API, the collection name and assistant names use hard coded defaults of default_collection and default_assistant respectively.
Step 4: Grant Required Permissions
In your project, AgentSpace runs under the Google-provided Discovery Engine Service Account with a name such as:
service-$PROJECT_NUMBER@gcp-sa-discoveryengine.iam.gserviceaccount.com
By default, this service account only has the Discovery Engine Service Agent role.
This is insufficient to invoke the Agent Engine ADK Agent and you may get the error “I’m sorry, it seems you are not allowed to perform this operation when invoking your ADK Agent in AgentSpace.
If you receive this error, grant the Vertex AI User role to the service account: e.g
PROJECT_ID=aviato-project-id
DISCOVERY_ENGINE_SA=service-123456789@gcp-sa-discoveryengine.iam.gserviceaccount.com
gcloud projects add-iam-policy-binding $PROJECT_ID \
- member="serviceAccount:$DISCOVERY_ENGINE_SA" \
- role="roles/aiplatform.user"
Troubleshooting
If you encounter any issues during deployment:
- Check Logs: The first step should always be to review the agent’s logs in Agentspace for detailed error messages.
- Verify Configuration: Double-check all configuration settings, especially environment variables and start commands.
- Dependencies: Ensure all required dependencies are correctly packaged with your agent.
- Network Issues: Confirm there are no network connectivity issues preventing communication with Agentspace.
- Agentspace Documentation: Refer to the official Agentspace documentation for specific troubleshooting guides and FAQs.
By following these instructions, you should be able to successfully deploy your Agent Engine agent to Google Agentspace.